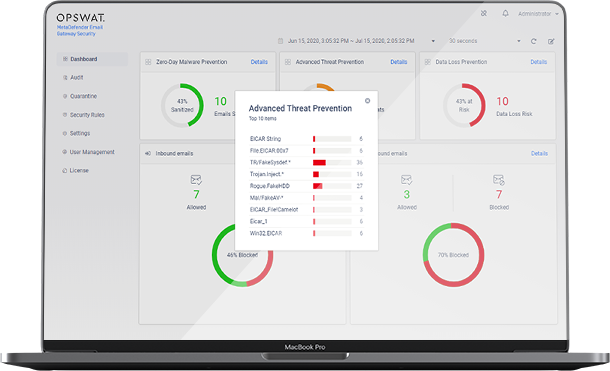
Compare the effectiveness of email security solutions
In this guide, you will learn:
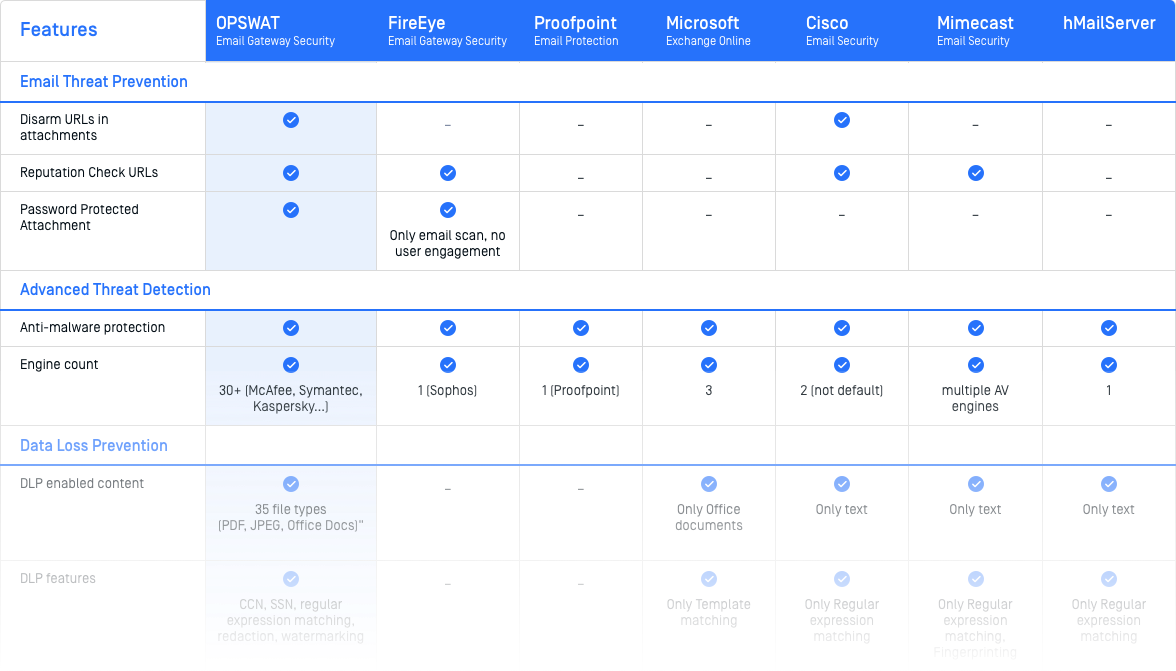
- Which solutions have the most effective anti-malware scanning
- Which solutions are able to remove malicious content from attachments
- How to fill ‘gaps’ in your current email security solution
Find the best product to keep your organization's inboxes secure
To help CISOs, IT and system administrators gain more control over email security, we put together this comparison guide to review how 7 leading vendors protect the major threat vectors.
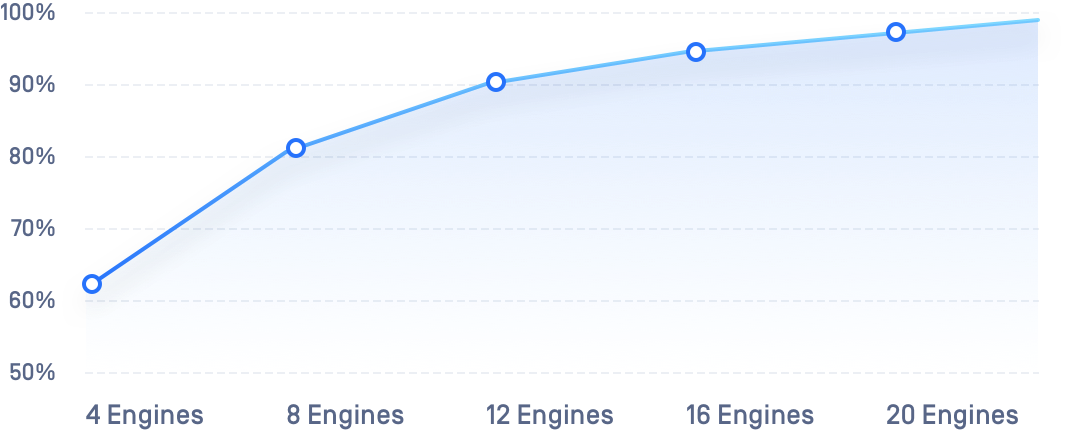
Increase threat detection rate up to 99.9%
4 steps to enhance your email security:
- Use prevention-based technologies to protect against zero-day attacks
- Scan all attachments with a minimum of 4 anti-malware engines
- Use CDR to disarm 80+ harmful file types
- Apply DLP to prevent sensitive content from accidentally entering or leaving your organization via emails
Get the Complete Comparison Guide